Expert IT Blog
Featured Article

The Dell AI Factory with NVIDIA: Creating an AI Environment that Turns Ideas into Practical Application
Bryan Samson Strategic Alliances Manager Technological Singularity “Technological Singularity,” or simply “the singularity” is a term I learned today. It is the advancement of artificial intelligence (AI) to where it can improve upon itself and therefore...
Recent Articles
IBM Power Systems Enhances the POWER9 Scale-Out Servers
Ron Gordon Director » Power Systems On July 14, IBM announced significant enhancements to the IBM Power Systems Scale-Out (SO) product line of the S914, S922, and S924 POWER9 servers. The new upgraded Power9 systems will begin shipping July 24, 2020. The servers...
VLOG: HPE InfoSight: AI-Driven for Intelligent Operations
3:25 HPE InfoSight: AI-Driven for Intelligent Operations Video Highlights Increases Infrastructure availability with Advanced Machine Learning Predicts and remediates 86% of issues without human intervention Cross Stack Analytics to determine issue in array or outside...
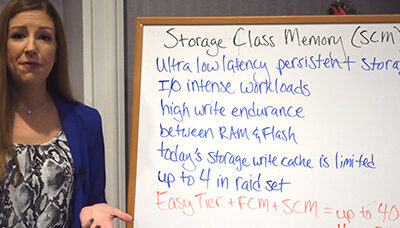
VLOG: IBM Storage Class Memory (SCM)
1:23 IBM Storage Class Memory (SCM) Storage-Class Memory (SCM) is ultra-low latency, persistent storage (NVMe) which combines the performance benefits of solid-state memory with the lower cost of conventional hard-disk magnetic storage. Laura Tuller, Mainline...
BLOG: NextGen Storage Virtualization
Robert Young Sr. Systems Engineer Data Storage Services Computing has evolved from Mainframe to Client-Server to the Third Platform, or Platform 3 as a co-worker (shout-out to Cuz!) described this computing paradigm. Basically, Platform 3 is mobile and cloud analytics...
Blog: Komprise: Managing the Unstructured Data Deluge
Ken Scott System Engineer Merriam-Webster defines the expression pack rat as “a person who collects or hoards especially unneeded items.” This definition also applies to IT professionals who insist on keeping all data handy for fear it may be needed to address a...
Blog: Alternative Programming Languages for z/OS Development
Introduction When many professionals in the Information Technology field think about mainframe development, they almost single-mindedly view it as a COBOL-only world. Although COBOL has dominated application development on IBM Z mainframe hardware, it is not...
BLOG: Benefits of IBM Z for Private Cloud
Kurt Repholz VP zSystems Sales In a recent Mainline blog, 2020 – The Year for Private Cloud on IBM Z, Red Hat OpenShift and IBM Cloud Paks for IBM Z’s private cloud were introduced. The beauty of the IBM Cloud Paks is the simplicity that Red Hat OpenShift with...
BLOG: IBM Storage Insights or Spectrum Control: Which is Right for Me?
Laura Tuller Systems Engineer, Storage Solutions Deciding between IBM Storage Insights and IBM Spectrum Control is a topic I’m often asked to discuss with end users and consultants. I’ve presented this very topic at IBM conferences with Bryan Odom, IBM Global...
BLOG: Improving Resiliency in Cybersecurity
Chris Dedham Software Sales Specialist The Convergence of Security and Data Management for Enhanced Cybersecurity Security breaches are usually about monetary gain for bad actors, which they accomplish by stealing data. Historically, security and...
BLOG: Benefits and Use Cases for IBM Cloud Pak for Integration
Joe Guthart Software Sales Specialist Container technology has fundamentally altered the development of software in today’s information technology environment. Who hasn’t heard about containers in the IT world? Nearly all of us have, and the containerized...
BLOG: HPE OneView: Your Software-Defined Infrastructure Foundation
Keith Thuerk Storage Engineer Modern data centers take on many forms, however the foundation for the most flexible designs are constructed utilizing Software Defined Infrastructure (SDI). Hewlett Packard Enterprise’s (HPE’s) modern data center management...
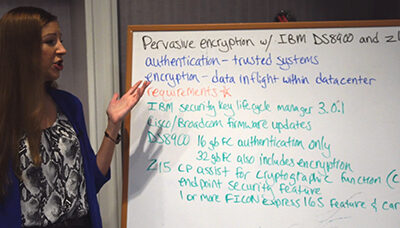
VLOG: Pervasive Encryption with IBM DS8900 and Mainframe z15
2:09 Pervasive Encryption with IBM DS8900 and Mainframe z15 Most companies find that just having application level encryption and data at rest encryption is not enough to ward off security threats. Pervasive Encryption provides a higher level of protection. ...