Bob Elliott
VP Storage Solutions
Customers are looking for help with new security challenges
Cybertheft. Malware. Hackers. Ransomware. It seems to be coming from all angles. Municipalities throughout the country have been, and still are facing the prospect of paying large ransoms from the massive disruptions cyber-attacks have caused their constituents.
IT teams are charged with protecting their company, their customers, themselves. GDPR brings with it new security requirements. While the United States has not addressed the issue as thoroughly as some (GDPR is a European Union initiative), there is still a lot of investments being made in cybersecurity. IBM has been focused on providing tools to face these challenges… making data storage easier and more responsive to threats of all kinds.
What is the IBM DS8000?
Legacy DS8000 Data Security Features
FlashCopy
The IBM DS8000 storage array was a pioneer in the use of instant copies of volumes or LUN’s to protect data from corruption and accidental (or intentional) deletion. A virtually identical copy was created using FlashCopy commands within the array, from a script or through automation using a pointer-based process. In other words, the array didn’t have to copy the data to create the new volume. Instead, a new set of pointers to the existing data created a virtual view of a new volume, using the original data. If desired, the data from the original volume was copied in the background to create a discrete new volume with its own copy of the data.
DS8000 FlashCopy was architected to be fast and lightweight. The pointer creation process took milliseconds, and while the optional data copy process could take time for a large volume, the FlashCopy output volume was available immediately. An option exists to use thin provisioned volumes as output volumes, which makes the process lightweight and space efficient.
However, there are limitations. While an individual copy is lightning fast, creating thousands of copies at once can begin to slow the process down. And, under the FlashCopy rules, up to 12 relationships can be linked to a source volume. That can be a problem – if you want to make many copies to give you the option of granular points in time for the recovery process. If you can make enough copies, the process becomes more like Continuous Data Protection (CDP) methodologies. Safeguarded Copy solves this problem and gives you an additional layer of protection from data compromise.
Building upon FlashCopy – Safeguarded Copy
As noted, FlashCopy allows up to 12 relationships per source volume, which limits the number of copies that can be made. The copies can be used to repair compromised data by picking one that is known to be safe and then reversing the relationship to restore the condition of the corrupted source volume. The current FlashCopy relationship limit does not provide much granularity of the points in time that can be used, which makes data recovery more cumbersome and time consuming. If the corruption is not recognized immediately, you may not even have a point in time to choose from.
Safeguarded Copy offers dramatically increased targets – up to 500 currently for a single source – providing far more granularity and longer time ranges to recover from. The technology also offers data protection beyond what was available with FlashCopy – a concept commonly referred to as immutability. The Safeguarded Copy is not a traditional volume – like a FlashCopy target volume is – and cannot be accessed directly. Therefore, it cannot be compromised or intentionally (or accidentally) deleted. Safeguarded Copy is used instead to recover data to a volume that will be mounted by the host and used for the recovery.
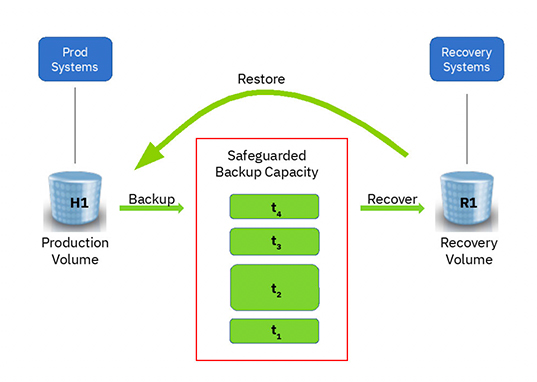
Another benefit over FlashCopy is that since a Safeguarded Copy is not a traditional volume, it also does not use logical volume slots. As you can imagine, making up to 500 copies for each of the hundreds of Production volumes would rapidly consume the entire logical addressing scheme of the array, as well as consume as many volume slots on the host. Safeguarded Copies are stored in a special pool of capacity called Safeguarded Backup Capacity (SGBC). Here is a graphical representation of the relationship between source volumes, SGBC and recovery volumes:
Data-At-Rest Encryption
What happens if an internal disk drive within the array fails? Normally, it is replaced, and the failed drive is returned to the supplying vendor. But what if the drive falls into the wrong hands? Or less likely but still possible, the entire array is compromised once it is returned after replacement? Data-at-rest encryption (DARE) is designed to protect you from the eventuality that a bad actor takes the drive or array and reverse engineers the data contained within it for ill intent. If encrypted while at rest (meaning once data is destaged onto the drive for periods of inactivity) then there is no way to recover the data for any purpose without an encryption key. The DS8000 encrypts the data within the array, utilizing AES 256-bit encryption. As it is destaged from the array cache, the array controller encrypts the data at line speed, meaning there is no performance impact from the encryption/decryption process. Likewise, when the data is recalled for use, the encrypted data is decrypted by the device controller on its way to the cache.
So, we see how technologies like FlashCopy and DARE protect data within the array. But what about protection for the data that comes from servers into the array or as it traverses the network outside of the array? Remote replication offers protection from site outages, but it poses the threat of compromised data once it exits the array. The DS8000 internal microcode addresses that threat with new capabilities contained in code Version 9.
Remote Replication
Technologies such as Metro Mirror and Global Mirror provide superior data protection from site outages. Metro Mirror provides synchronous copy at longer distances (300km is supported with farther distances possible) with lower overhead than competing technologies. In partnership with the ability for a failing array to switch to a backup array, known as Hyperswap, data recovery can be achieved with no impact to application processing. Global Mirror provides asynchronous copy at 3-5 seconds of data lag under most circumstances, with far less impact to the infrastructure than competing technologies. By utilizing a unique bitmapping process instead of cache or journaling techniques, data lag is minimal. The process is protected from outside events such as flooding of the primary site with unanticipated write activity or transmission disruption of the remote links.
Both Metro Mirror and Global Mirror can be related in various configurations, with up to four site protection to provide the utmost backup and recovery flexibility. IBM provides software called Copy Services Manager to make the entire FlashCopy/remote replication experience a simple and automated “point and click” process. Globally Dispersed Parallel Sysplex can provide a bulletproof Business Continuance framework which can provide zero downtime capability, without distance limitations.
Fibre Channel Endpoint Security – Link Authentication and Encryption
The latest DS8000 model, DS8900, utilizes a new 32gb Fibre Channel/FICON adapter that supports both link authentication and encryption of data-in-flight. As data arrives at the Fibre/FICON port at the front of the array, the adapter logic requires authentication from a key server to be granted access into the array. Key servers can be the IBM Security Key Lifecycle Manager (SKLM), which can also be run inside a container using z/OS2.4 Container Extensions. Or, any KMIP-compliant key manager, such as Safenet KeySecure can be employed.
For encryption of data-in-flight (EDiF), the port adapter provides for endpoint security with the FC-SP-2 encryption method. As with DARE, there is no performance impact of the port adapter providing encryption/decryption services. With EDiF, data is no longer at risk of being hacked or otherwise compromised once it leaves the array.
Summary
As a leader in the Enterprise Storage market segment, the DS8000 has been proven to provide the highest levels of security with the broadest array of data protection technologies. IBM continually develops these technologies as market conditions demand them. The architecture of the DS8000 enables rapid development cycles with minimal disruption to the proven reliability track record that IBM is famous for.
Related articles:
IBM DS8880 Safeguarded Copy Redbook
Blog: Does Wanna Cry Have Your Organization in Tears?
Learn more about Hybrid Storage Solutions
More Information
Please contact your Mainline Account Executive directly for additional information, or click here to contact us with any questions..

